Now and then, while performing internal penetration tests we come across Splunk default installs where system users can log in as “admin” and are granted the associated privileges without having to authenticate. Splunk is based on Django, and among the options it gives you when accessing the admin panel is one that is particularly attractive from an attacker’s point of view: Apps. Splunk allows installing custom apps from a number of sources, including from a local file, as shown below:
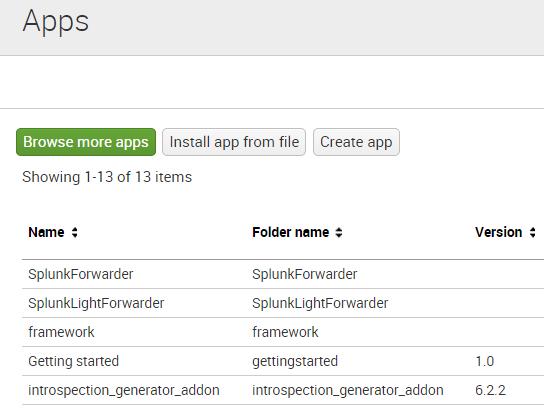
During the last internal penetration test I carried out, I found one of these Splunk admin panels. After searching around for a bit I could not find a web shell that would successfully allow me to execute system commands when I uploaded it through the “custom app install” option – so I developed a simple but useful one of my own. Splunk apps need to follow Django conventions regarding the files needed and their structure, and most of the time they also make use of Splunk’s API. The documentation is quite good, so it didn’t take me too long to figure it out. After writing the code, I had to convert the app folder to .tar.gz, as this is the format, along with .zip, that Splunk expects. After that, all I had to do was click on the “Install app from file” and
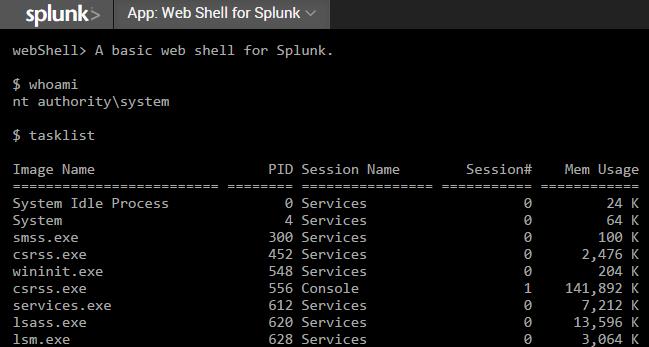
follow the instructions. Once the app has been successfully installed, this is what it looks like when you access it:
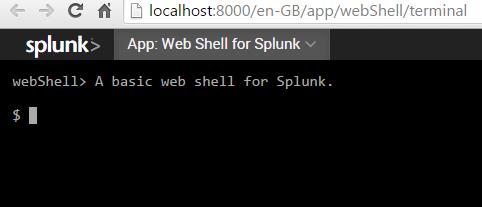
The interface is quite nice, as I used JQuery’s terminal emulator to make it a little bit more user friendly than the typical “?CMD=” GET-request-based web shell. Below is a screenshot of the app running a couple of commands. 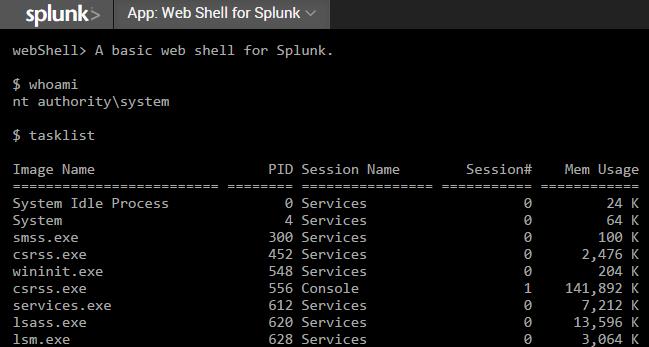
Please note that as it is configured at the moment, the app requires access to the admin panel first. This was done on purpose to avoid random access to the web shell, but this is easily modifiable in the source code if the situation requires it. The source code as well as the ready to go .tar.gz files can be found at: https://github.com/Dionach/Splunk-Web-Shell
Like what you see? Share with a friend.
