Penetration testing should be part of a preventative approach to Information Security and Security Control to ensure that vulnerabilities are not exploited.
It is still a mystery as to why a large number of organisations do not take a more preventative approach to Information Security. There has been enough information in various publications about the cost associated in dealing with security breaches. The cost aside, the general knowledge and acceptance that we are under constant cyber-attacks from both known and unknown parties would surely be enough for companies to seek independent advice.
It was very reassuring to come across a blog entry from a company involved in the gaming industry (https://blog.phonicuk.com/post/2013/05/17/McMyAdmin-to-undergo-external-p… ).
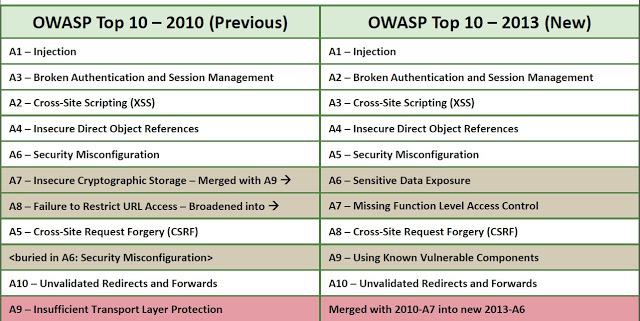
This company had clearly identified potential threats and had publically acknowledged the need for independent verification that their application was not susceptible to the most common application vulnerabilities, such as the OWASP top ten (https://www.owasp.org/index.php/Category:OWASP_Top_Ten_Project).
Why do only a minority of companies approach security in this way?
This is not a subject that any of us should feel ashamed to openly discuss. In most cases, companies have similar issues relating to security. By openly discussing them we may go some way to reducing them. The Data Protection Act requires that technical measures should be taken against unauthorised processing of personal data. Although it doesn’t state penetration testing as a direct solution, it would be difficult to judge that these measures are in place without some technical compliance checking, such as penetration testing.
A penetration test (or Pen Test) is a commonly accepted way to identify vulnerabilities within infrastructures and applications. When pen tests are completed thoroughly and by a recognised pen testing company, the result of such a service should be a well written, concise report outlining the issues, proof of concepts and most importantly, practical recommendations.
Dionach’s objective is to assist clients in ensuring that their critical IT infrastructure and applications are adequately protected. This is achieved not through the insistence that a device will solve all of their problems, but through open consultation and discussions. We identify specific threats which we feel the client may be subject to and advise them of threats they may not have considered.
Is cost a reason not to be preventative?
The cost of pen testing is generally based upon the size of the infrastructure or application involved. In most cases the cost is less than people realise, especially when compared as a percentage to an organisation’s annual hardware and software costs. As a recent Government report outlines, the costs associated with a breach are generally much greater than the costs of conducting testing in the first place. Further to this, failure to take adequate steps to ensure your environment is not susceptible to attacks, may result in your organisation not being able to operate or be responsible for the loss of personal data.
The alternative is to pretend that everything is ok and forget we are subjected to countless attacks each day and deal with the consequences after the fact. One important question when choosing this approach must be, can our organisation or brand handle the fall out?
Like what you see? Share with a friend.




